Featured
Table of Contents
What Is Ipsec And How It Works
These settlements take two types, main and aggressive. The host system that starts the process recommends file encryption and authentication algorithms and settlements continue till both systems settle on the accepted protocols. The host system that starts the procedure proposes its preferred file encryption and authentication techniques but does not work out or change its choices.
When the data has actually been transferred or the session times out, the IPsec connection is closed. The personal secrets used for the transfer are erased, and the process comes to an end.
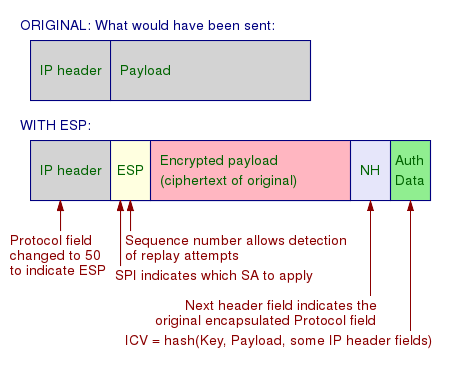
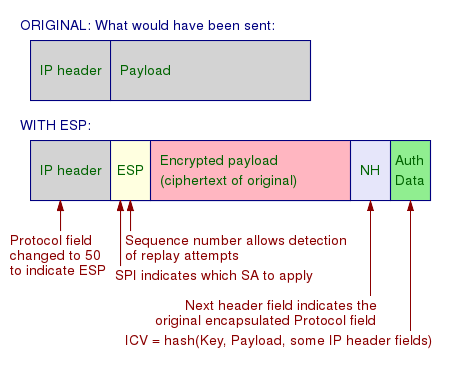
IPsec utilizes two primary protocols to provide security services, the Authentication Header (AH) procedure and the Encapsulating Security Payload (ESP) protocol, in addition to a number of others. Not all of these protocols and algorithms need to be utilized the specific selection is identified throughout the Negotiations stage. The Authentication Header procedure confirms information origin and integrity and provides replay protection.
Ipsec Configuration - Win32 Apps
A relied on certificate authority (CA) supplies digital certificates to confirm the interaction. This enables the host system receiving the data to verify that the sender is who they declare to be. The Kerberos protocol offers a central authentication service, allowing devices that use it to validate each other. Various IPsec applications might utilize various authentication techniques, but the outcome is the exact same: the secure transference of data.
The transportation and tunnel IPsec modes have numerous key distinctions. Transport mode is primarily utilized in scenarios where the two host systems communicating are trusted and have their own security treatments in location.
File encryption is applied to both the payload and the IP header, and a new IP header is contributed to the encrypted package. Tunnel mode offers a secure connection in between points, with the initial IP package wrapped inside a brand-new IP package for extra protection. Tunnel mode can be used in cases where endpoints are not relied on or are lacking security systems.
Ipsec Vpn In Details - Cyberbruharmy - Medium
This suggests that users on both networks can communicate as if they remained in the same area. Client-to-site VPNs enable individual gadgets to link to a network remotely. With this alternative, a remote employee can run on the very same network as the rest of their team, even if they aren't in the exact same place.
(client-to-site or client-to-client, for example) most IPsec geographies come with both benefits and downsides. Let's take a more detailed look at the advantages and downsides of an IPsec VPN.
An IPSec VPN supplies robust network security by encrypting and validating data as it travels between points on the network. An IPSec VPN is versatile and can be configured for different usage cases, like site-to-site, client-to-site, and client-to-client. This makes it a good alternative for companies of all shapes and sizes.
Ipsec And Ike
IPsec and SSL VPNs have one primary distinction: the endpoint of each protocol. An IPsec VPN lets a user connect remotely to a network and all its applications.
For mac, OS (by means of the App Shop) and i, OS variations, Nord, VPN uses IKEv2/IPsec. This is a combination of the IPsec and Internet Secret Exchange version 2 (IKEv2) protocols. IKEv2/IPsec permits a secure VPN connection, without jeopardizing on web speeds. IKEv2/IPsec is just one alternative offered to Nord, VPN users, however.
Stay safe with the world's leading VPN.
What Is Ipsec And How Does It Work?
Before we take a dive into the tech stuff, it is very important to see that IPsec has quite a history. It is interlinked with the origins of the Internet and is the outcome of efforts to develop IP-layer encryption techniques in the early 90s. As an open protocol backed by constant development, it has proved its qualities over the years and although challenger procedures such as Wireguard have actually emerged, IPsec keeps its position as the most widely used VPN protocol together with Open, VPN.
SAKMP is a protocol used for developing Security Association (SA). This procedure includes 2 steps: Stage 1 develops the IKE SA tunnel, a two-way management tunnel for key exchange. When the interaction is developed, IPSEC SA channels for safe and secure data transfer are developed in phase 2. Qualities of this one-way IPsec VPN tunnel, such as which cipher, method or secret will be utilized, were pre-agreed by both hosts (in case of IPsec VPN, this is a connection between a gateway and computer).
IPsec VPNs are widely used for several factors such as: High speed, Extremely strong ciphers, High speed of establishing the connection, Broad adoption by running systems, routers and other network devices, Of course,. There are alternative options out there such as Open, VPN, Wireguard and others (see the list of important VPN procedures on our blog).
About Virtual Private Network (Ipsec) - Techdocs
When developing an IKEv2 connection, IPsec uses UDP/500 and UDP/4500 ports by default. By standard, the connection is developed on UDP/500, but if it appears throughout the IKE establishment that the source/destination is behind the NAT, the port is switched to UDP/4500 (for details about a method called port forwarding, check the article VPN Port Forwarding: Great or Bad?).
There are numerous distinctions in terms of innovation, use, advantages, and disadvantages. to encrypt HTTPS traffic. The purpose of HTTPS is to secure the content of interaction in between the sender and recipient. This guarantees that anybody who wishes to intercept interaction will not have the ability to discover usernames, passwords, banking details, or other sensitive information.
All this info can be seen and kept track of by the ISP, federal government, or misused by corporations and assailants. To remove such threats, IPsec VPN is a go-to option. IPsec VPN works on a various network layer than SSL VPN. IPsec VPN operates on the network layer (L3) while SSL VPN operates on the application layer.
Internet Protocol Security (Ipsec)

When security is the main issue, modern cloud IPsec VPN need to be selected over SSL given that it secures all traffic from the host to the application/network/cloud. SSL VPN protects traffic from the web browser to the web server just. IPsec VPN safeguards any traffic between 2 points identified by IP addresses.
The issue of selecting in between IPsec VPN vs SSL VPN is carefully associated to the subject "Do You Need a VPN When A Lot Of Online Traffic Is Encrypted?" which we have covered in our current blog site. Some may believe that VPNs are barely essential with the increase of inbuilt encryption directly in e-mail, web browsers, applications and cloud storage.
Latest Posts
Best Business Vpn In 2023 [Ranked & Reviewed]
Best Business Vpn Options In 2023 [Keeping Smb Data ...
Best Remote Access Vpn In Usa To Work From Home